Over the past several months, it has become clear that the Internet and
our Privacy have been fundamentally compromised. A Private search engine
DuckDuckGo
claims that when you click on one of their search results, they do not
send personally identifiable information along with your request to
the third party.
Like Google dorks (advance search patterns), there are thousands of
similar, but technically more useful search hacks are also available in DuckDuckGo called DuckDuckGoodies. Today I am going to share about Handy "Cryptography" using DuckDuckGo search engine.
Whether you are a Hacker, Cracker or a Researcher, you need to face a
number of hash strings in your day to day life. Hashing is a one way encryption
of a plain text or a file, generally used to secure passwords or to
check the integrity of the file. There is a certain set of hashing
algorithms, e.g.md5, sha1, sha-512 etc.
A hash function generates the exact output if executed n number
of times with the same input. If there is a very small change in the
input, there will be a difference between the two outputs.
Duckduckgo is a search engine which gives you a flexibility to perform
such operations. It enables user to generate the hash of strings, find
the algorithm used for generating a hash, give other equivalent hashes
of certain hash input.
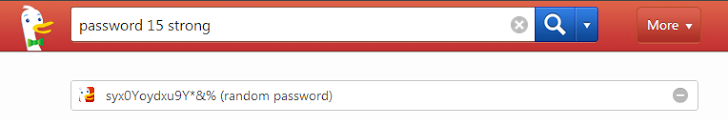
1.) Generating a Strong Password: The security and integrity of
our passwords are a constant battle. The password is the only lock which
can make your private information more secure. One of the biggest
reasons why people use weak passwords is usually a combination of
convenience, and the ability to recall them easily. But using a weak
password is the equivalent to installing a lock on your front door that
you could open with a Popsicle stick.
Last year, we reported that hackers managed to crack 16-character alphanumeric password
in less than an HOUR. No password is foolproof, but by using a long,
unique and strong password you can make your password complicated enough
to slow down password cracking programs. DuckDuckGo provides you a feature of generating a strong password instantly.
Search Term: password 15 strong
Where 15 is the password length.
2.) Generating a Hash: Hashing makes it difficult for an attacker
to retrieve the original plain text string back from the encrypted
password and it lets sites keep a list of hashes, rather than plain text
passwords.
Using DuckDuckGo's Handy option, you can generate a hash value of any
string just by using the following syntax on the search engine.
md5 TheHackerNewssha512 TheHackerNewssha TheHackerNewssha224 TheHackerNewssha256 TheHackerNewssha384 TheHackerNews
Where TheHackerNews is the plain text string and md5 or sha is the hashing algorithm.
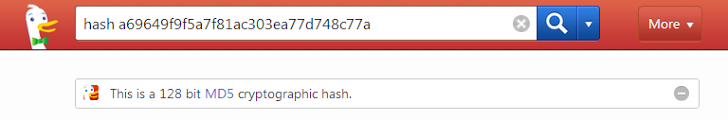
3.) Identifying Hash Algorithm: Manual finding of the
algorithm used for generating the hash is a tedious task. DuckDuckGo
provides you an inbuilt hash identification tool, which allows you to
identify the hashing algorithm used for generating the hash string given
as input.
hash a69649f9f5a7f81ac303ea77d748c77a
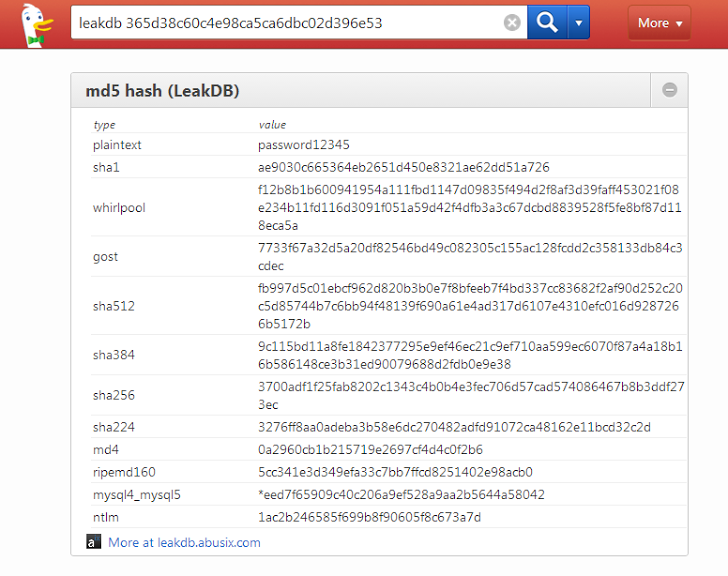
4.) Finding Plain text from Hashes: One more great feature
provided by DuckDuckGo search engine is that it gives you plain text
value and equivalent hash code in other algorithms. DuckDuckGo is not
cracking hashes for you, but actually matches the hash value of the
previously leaked database archive.
Tor exit enclave: DuckDuckGo also operates a Tor exit enclave, which basically means that if you’re using DuckDuckGo through the Tor anonymity tool, you will achieve end-to-end anonymous, encrypted search that is faster than what you might expect with Tor browsing, alone.
Want more Interesting News like this? Sign up here to receive the best of 'The Hacker News' delivered daily straight to your inbox.
Read Next — Related Articles:
Subscribe for Updates
Latest Stories
 How To Encrypt Your USB Drive to Protect Data
How To Encrypt Your USB Drive to Protect Data IT Security – Do it the hard or easy way!
IT Security – Do it the hard or easy way! Do You also want to Hack Facebook Account of your Girlfriend?
Do You also want to Hack Facebook Account of your Girlfriend? I keep 200+ Browser Tabs Open, and My Computer Runs Absolutely Fine. Here’s My Secret.
I keep 200+ Browser Tabs Open, and My Computer Runs Absolutely Fine. Here’s My Secret. Why We Love Android M (And You Should, Too!)
Why We Love Android M (And You Should, Too!) Apple Mac OS X 10.11 'El Capitan' Update unveiled at WWDC 2015
Apple Mac OS X 10.11 'El Capitan' Update unveiled at WWDC 2015 Python for Security Professionals: Free IT Security Training
Python for Security Professionals: Free IT Security Training Is China Behind the Massive Data Theft of 4 Million U.S. Officials?
Is China Behind the Massive Data Theft of 4 Million U.S. Officials?Comments